You wake up at 2:00 AM to grab a glass of water. As you walk past your teenager’s bedroom, you notice the faint, distinct blue glow of a screen reflecting under the door. The next morning, they are exhausted and struggling to focus. You open your standard parental controls dashboard and check the logs. According to Google FamilyLink, the device was locked at 10:00 PM. You tap the locate your phone feature, and it shows the device sitting exactly where it should be—on their nightstand. So, what exactly happened between midnight and morning?
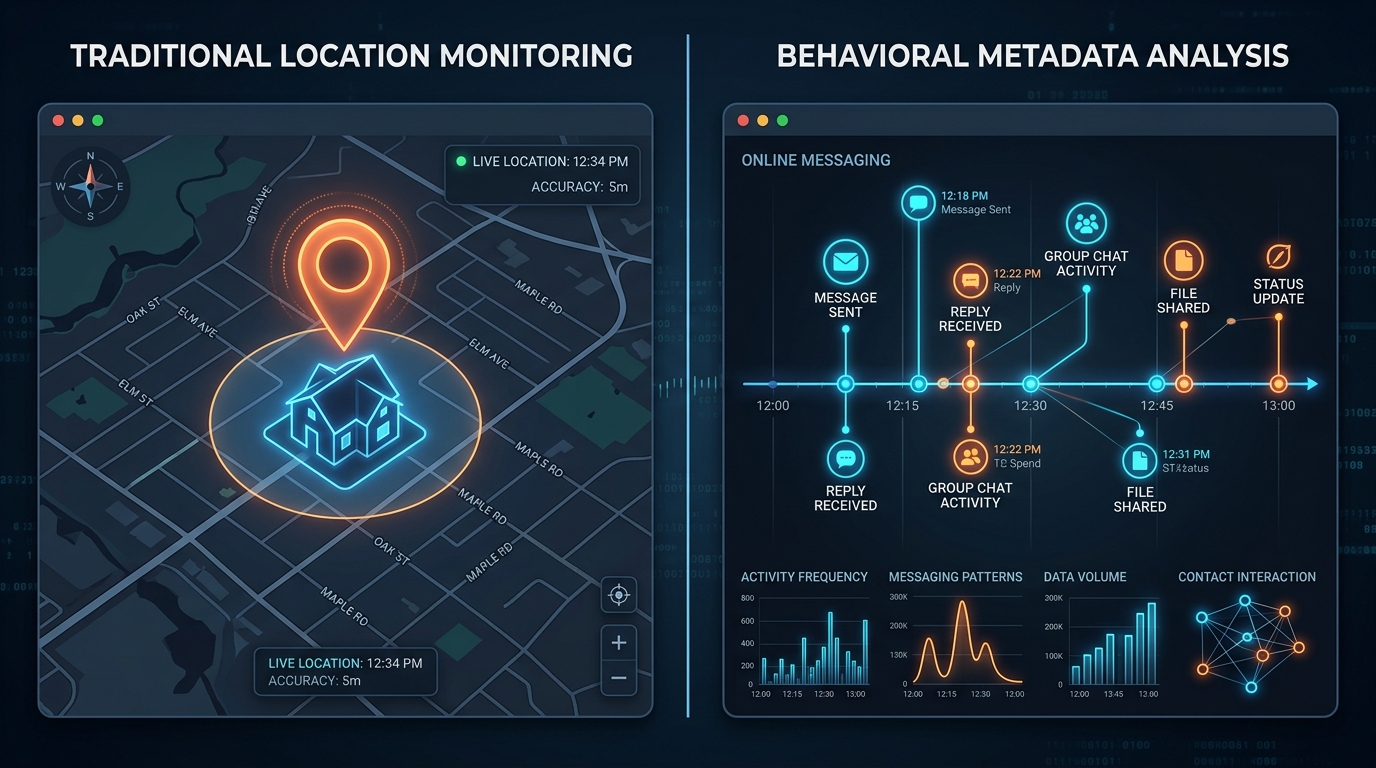
Modern family digital safety requires comparing physical device restrictions directly against behavioral activity monitoring. While traditional parental controls rely on locking specific hardware or tracking GPS coordinates, messaging activity trackers analyze when and how long a user is online across multiple platforms, providing a clearer picture of digital habits without actually reading private messages.
In my daily work as a software developer specializing in natural language processing and AI chatbots, I spend a lot of time looking at how humans communicate. Text data is only one part of the equation. Often, the metadata—the timestamps, the session frequency, the multi-device handoffs—tells a far more revealing story about human behavior. When we apply this technical perspective to family safety, the contrast between old methods and current digital realities becomes clear.
Physical location metrics cannot monitor digital curfews
For years, the standard approach to family monitoring relied heavily on spatial data. You install a family safety app, and it pings a server to tell you if a device has left the school zone.
The Traditional Approach: A parent opens a map interface to verify physical safety. If the dot is inside the house, the assumption is that the child is safe and presumably asleep.
The Modern Reality: Physical presence no longer equals digital safety. A teenager might be physically safe in their bed but actively chatting with strangers on a secondary device. Furthermore, device-level lockouts are relatively easy to bypass. A smart kid will simply open WhatsApp Web or Telegram Web on a school-issued laptop after their main Android device goes into lockdown mode. The physical location tool registers zero movement, completely missing the three hours of active messaging.

Reactive background searches answer the wrong safety questions
When unknown numbers pop up on a family device, parents often rely on a patchwork of search tools. This approach attempts to solve digital safety reactively rather than proactively.
The Reactive Method: You see a strange number on a caller ID or a notification. You immediately look for a free phone number look up tool. You might try a backwards phone number lookup or use a spy dialer service to figure out who is trying to contact your child. These reverse phone number search free queries can occasionally identify a telemarketer or a known scammer.
The Proactive Method: Knowing who called once is far less useful than knowing how often your family member is active online. A sporadic unknown call is an annoyance; a persistent pattern of being online at 3:00 AM on a customized GB WhatsApp install or the Telegram app indicates a behavioral shift. Reactive lookups are a single-use fix, whereas tracking daily activity windows establishes a baseline for healthy routines.
Multi-platform architecture is replacing single-channel tracking
The industry is shifting away from analyzing isolated data streams. Recent data suggests that attempting to monitor digital behavior through a single channel is increasingly ineffective.
According to the Mobile App Trends 2024 report published by Adjust, global app sessions increased by 7% year-over-year, and consumer spending pushed past the $167 billion mark. The report highlights that effective measurement now depends heavily on multi-platform architecture rather than single-channel data points.
Families are facing this exact same technical challenge.
If you only monitor an iPhone’s screen time, you miss the tablet. If you only restrict SMS, you miss the instant messaging platforms. As my colleague Deniz Yılmaz has noted regarding multi-platform tracking, understanding modern digital habits requires analyzing cross-platform synchronization. You need to see the complete timeline, bridging the gap between mobile sessions and desktop web clients.
Privacy expectations demand metadata analysis over invasive reading
One of the hardest balances to strike in family monitoring is maintaining trust while ensuring safety. Comparing invasive message reading against metadata analysis shows why the latter is more sustainable.
The Invasive Approach: Demanding passwords, physically confiscating phones to read chat logs, or installing hidden screen-recording software. This often damages trust. Furthermore, privacy expectations are shifting. The same Adjust report noted that iOS users opting into App Tracking Transparency (ATT) increased from 35% to 38%. Even younger users are becoming highly protective of their personal data.
The Metadata Approach: Instead of reading what is being said, you monitor the timestamps of when they are saying it. This is exactly what Seen: WA Family Online Tracker is designed to handle. It focuses directly on WhatsApp and Telegram last seen data. By observing when a profile comes online and when it goes offline, the app builds an activity graph. You do not need to read private conversations to know that a teenager was awake and messaging for two hours past their bedtime.

Native performance and reliability dictate long-term adoption
The final comparison rests on usability. The tools parents use must work reliably without hindering the device's performance.
Heavy Interception Tools: Apps that attempt to intercept every keystroke or continuously stream GPS data drain battery life aggressively. They slow down the target device, leading to friction. User behavior data suggests that nearly 70% of users will delete an application after the first use if it severely impacts device speed or battery life.
Lightweight Analytics: Cloud-based metadata trackers operate independently of the target device’s processor. Since tools like Seen operate by observing public network status signals rather than running heavy background processes on the child's phone, they avoid battery drain completely.
If you want to move away from constant arguments over devices, establishing transparent rules based on objective activity data is a logical step. Understanding the technical difference between enforcing a physical lock and observing a behavioral pattern allows parents to address the actual issue: sleep deprivation and digital boundaries. We build tools at ParentalPro Apps precisely because capturing the right signals—without crossing the line into privacy invasion—fosters healthier communication.